
Amazon SNS and SES are SMS and email sending services. These are a juicy target for attackers, and frequently targeted when an access key leaks. Based on CloudTrail logs, we have identified malicious actors and toolsets abusing these services. Additional OSINT led us to discover a phishing campaign impersonating official French Government websites!
Enforce IMDSv2 at the region level in AWS
AWS has recently released a new feature to enforce IMDSv2 by default at the region level. As we're continuously striving to make cloud security a better place for everyone, we've submitted a pull request to add support in the Terraform AWS provider - stay tuned!
SEE THE ANNOUNCEMENTDiscover cross-account attack paths in AWS environments with WithSecure's IAMGraph
The team at WithSecure, an UK-based consultancy shop, has recently released IAMGraph. Based on the Z3 Theorem Prover, it analyzes IAM policies and maps cross-account accesses into a Neo4j graph database that you can easily query.
DISCOVER IAMGRAPH
Keep Hackers Out of Your Clusters With These 5 Simple Tricks!
At KubeCon EU, Christophe Tafani-Dereeper and Frederic Baguelin presented a threat-informed roadmap to secure Kubernetes clusters.
WATCH THE TALK
Live next week on the Cloud Security Podcast by Google!
Our very own Zack Allen, leading Datadog's security research efforts, will be chatting with Google's Anton Chuvakin on their well-known Cloud Security Podcast. Expect some exciting bits about detecting threats in cloud environments!
ATTEND THE PODCASTSecurity Feature Releases
Kubernetes Security Posture Management (KSPM)

In recent years, the popularity of Kubernetes deployments has surged—as has the prevalence of security risks associated with the technology. Red Hat’s State of Kubernetes Security for 2023 reveals that 67 percent of organizations have encountered delays in application deployments due to Kubernetes-related security issues.
That’s why we are excited to introduce our new Kubernetes Security Posture Management (KSPM) capabilities, which are available within Datadog Cloud Security Management (CSM).
KSPM helps you proactively strengthen the security posture of your Kubernetes deployments by benchmarking your environment against established industry best practices, such as those defined by CIS, or your own custom detection policies.
Check out our KSPM documentation to get started, or head to the Frameworks page in Datadog CSM.
SCA Extends to the CI

Datadog is proud to announce the launch of Datadog SCA (previously Application Vulnerability Management). This represents an expansion of our Datadog Application Security capabilities to help teams leverage open-source with confidence, from source code, to production services.
Datadog SCA helps you track and manage the open-source libraries within your applications, including security risks (malware and vulnerabilities), business risk (SBOM), and licensing.
Our secret sauce is our end-to-end coverage: Datadog SCA analyzes your libraries as early as when developers commit code (new in Beta), and all the way to the existing production applications (Generally Available), even without access to the source code. Also, our prioritization system takes into account the entire context, reducing the number of alerts and increasing your productivity.
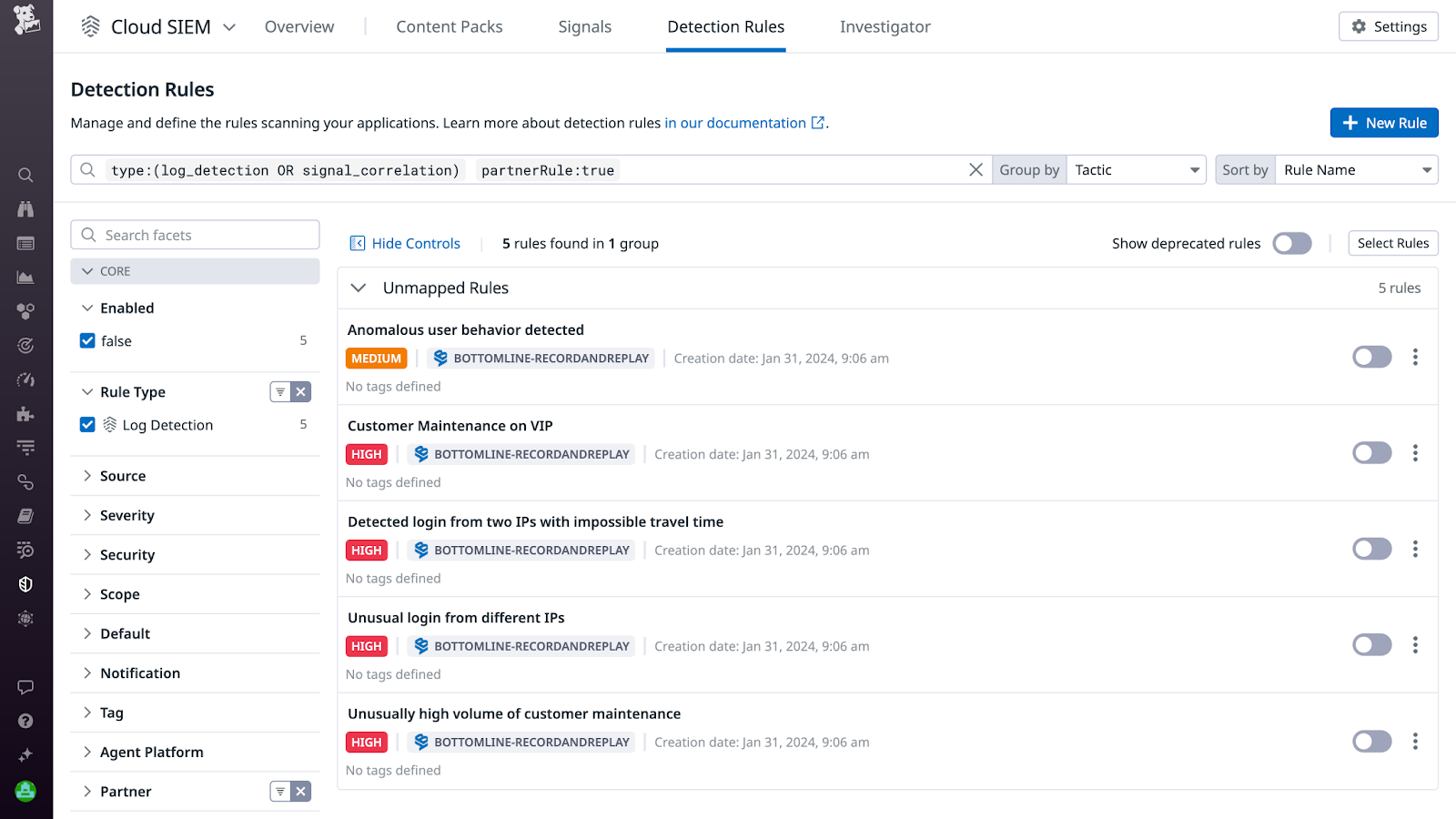
SIEM Detection Rules expanded to Security Partners
Datadog Technology Partners can now seamlessly integrate OOTB SIEM detection rules into their solutions, broadening Cloud SIEM coverage for existing customers and delivering enhanced out-of-the-box security against diverse threats.
LEARN MORE
90 days of deleted historical views in Log Rehydration
Forward security alerts from external vendors or apps to Datadog Cloud SIEM with the third party detection method.
VIEW THE SUPPORT DOCUMENTATION